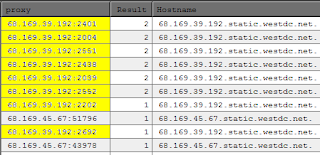
The highlighted address was listening on two ports at the same time, but had also been seen on no less than six other ports during the same run. The non-highlighted address was also listening on two distinct ports. Those ports will eventually close and both addresses will reappear sooner or later on different ports.
This is more annoying than it is useful.
So what the hell is going on here? I haven't done my homework yet, but I still have a gut feeling these are TOR nodes. Of course, at one time I had a gut feeling all those Chinese proxies were malware, but we all saw how that turned out.
There are about 9,000 of these multi-port SOCKS4 proxies that have showed up since I started doing SOCKS back in March. So many that I'm going to start flagging them on the list this weekend.
UPDATE 05/20/2011
I was somewhat surprised to see the number of plain old CERN proxies that were also running on floating ports, but they're still far outnumbered by the SOCKS floaters.
Since these SOCKS4 floaters seem to be as ephemeral as Chinese proxies, and therefore more trouble than they're worth, I am considering re-checking them between list publishing runs to keep their numbers down. It doesn't help anyone to list them if they've moved on to another port.
this ip address are too wick to post classifieds pleasse can you add their powers
ReplyDelete